[ad_1]
Join leaders in Boston on March 27 for an exclusive night of networking, insights, and conversation. Request an invite here.
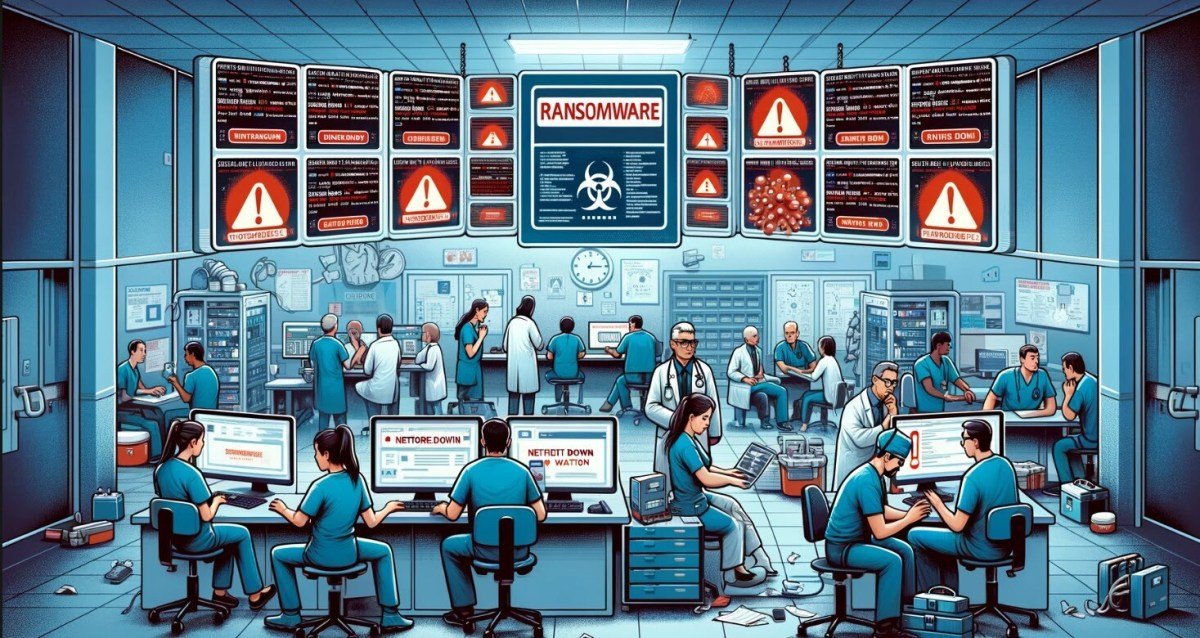
Healthcare supply chains are facing a digital pandemic, with the latest UnitedHealth Group breach showing the power of an orchestrated ransomware attack to shut down supply chains.
Attackers hope to create chaos quickly to force their victims to pay exceptionally high ransoms fast. With human lives on the line, healthcare supply chains are a prime target. United Healthcare paid the $22 million ransom in Bitcoin, visible on the digital currencies blockchain. BlackCat, or ALPHV led the cyberattack, taking credit for it on their website and then quickly deleting its mention. A dispute over how the ransom would be divided led one of the attackers to accuse AlphV on their cybercriminal underground forum RAMP that they’d been cheated out of their fair share.
The attacks’ impact continues to reverberate through regional and national healthcare supply chains, causing widespread financial chaos. The New York Times reports how far-reaching the attacks’ impact is on everyone from patients to physicians attempting to continue operating despite approvals, reimbursements and payments on hold or non-existent.
Healthcare is facing a digital pandemic
It’s the most severe cyberattack in the history of healthcare, further validating just how vulnerable the industry is to an ongoing digital pandemic of breaches and ransomware attacks. The Health and Human Services HHS Breach Portal quantifies how healthcare’s digital pandemic continues to grow as attackers sharpen their tradecraft on the industry. Eighteen percent of healthcare employees are willing to sell confidential data to unauthorized parties for as little as $500 to $1,000, according to an Accenture study.
Change Healthcare, the unit hit by the attack reports that more than 113 systems are still affected by the attack this morning in their automated alerts. UnitedHealth Group filed an 8K with the Securities and Exchange Commission on Feb. 21, explaining the attack and also providing a link to updates.
Health and Human Services (HHS) has seen this coming. Their Office of Information Security has produced reports and presentations explaining cyber threats in detail. Earlier this year, they published a comprehensive 50-page presentation on ransomware and healthcare.
Merritt Baer, the advisor to expanso.io and balkanID and former CISO, told VentureBeat that “ransomware groups love supply chain attacks– we see evidence of this in their high profile targets, from Kaseya to SolarWinds. And it makes sense: they target entities that have a role in a supply chain to get outsized impact. In other words, those embedded in a supply chain have downstream customers and those customers have their own downstream customers.” Baer emphasized to VentureBeat that “ransomware groups are looking for victims that will pay. In a regulated space like healthcare, we’re talking about both a business and regulatory costs that lead them to want to pay.”
Where Healthcare Providers Need To Start
Ransomware attack strategies are becoming more challenging to identify and stop, accelerated by Ransomware-as-a-Service (RaaS) groups actively recruiting specialists with common Windows and system admin tools expertise to launch attacks traditional security solutions struggle to identify. Attacker’s favorite tradecrafts include living-off-the-land (LotL) attacks and those that harvest identities off of endpoints by finding gaps in endpoint defenses. LotLs are attacks that are launched using common tools so they can’t be tracked easily.
Baer observes that “from a technical perspective, remember that with Ransomware as a Service (RaaS), folks can “rent” the apparatus to enact ransomware, on the black market– so you don’t even have to be very good to be able to pwn an entity.”
“Threat actors are increasingly targeting flaws in cyber hygiene, including legacy vulnerability management processes,” Srinivas Mukkamala, chief product officer at Ivanti, told VentureBeat. CISOs say they are least prepared to defend against supply chain vulnerabilities, ransomware and software vulnerabilities. Just 42% of CISOs and senior cybersecurity leaders say they are very prepared to safeguard against supply chain threats, with 46% considering it a high-level threat.
Healthcare CISOs and their teams need to consider the following strategies for getting started:
Complete a compromise assessment first and consider an incident response retainer. Healthcare IT Strategy Consultant and former CIO Drex DeFord says that healthcare CISOs must first establish a baseline and ensure a clean environment. “When you have a compromise assessment done, get a comprehensive look at the entire environment and make sure that you’re not owned, and you just don’t know it yet is incredibly important,” DeFord told VentureBeat. DeFord also advises healthcare CISOs to get an incidence response retainer if they don’t already have one. “That makes sure that should something happen, and you do have a security incident, you can call someone, and they will come immediately,” he advises.
Eliminate any inactive, unused identities in IAM and PAM systems right away. To remove dormant credentials, do a hard reset on every IAM and PAM system in the tech stack to the identity level. They lead cyber attackers to IAM and PAM servers. First, remove expired account access privileges. Second, limit user data and system access by role by resetting privileged access policies.
Ensuring that BYOD asset configurations are up-to-date and compliant. Most of the security teams’ endpoint asset management time goes to updating and compliant corporate-owned device configurations. Teams don’t always get to BYOD endpoints, and IT departments’ policies on employee devices can be too broad. CISOs and their teams are starting to rely more on endpoint protection platforms to automate the configuration and deployment of corporate and BYOD endpoint devices. CrowdStrike Falcon, Ivanti Neurons, and Microsoft Defender for Endpoint, which correlates threat data from emails, endpoints, identities, and applications, are leading endpoint platforms that can do this at scale.
Enable multi-factor authentication (MFA) for every validated account. Attackers target the businesses that healthcare providers frequently do business within an attempt to obtain credentials for privileged access and identity theft, which allows them to access internal systems. The more privileged an account has, the more likely it is to be the target of a credential-based attack. Implement MFA for all external business partners, contractors, suppliers, and employees as a first step. Be rigorous about canceling credentials that third parties don’t need.
Reduce ransomware risk by automating patch management. Automation relieves IT and desk staff from the heavy workloads they already have supporting virtual workers and high-priority digital transformation projects. Sixty-two percent of IT and security professionals procrastinate on patch management because 71% think patching is too complicated and time-consuming. Moving beyond inventory-based patch management to AI, machine learning, and bot-based technology that can prioritize threats is their goal. Ivanti Neurons for Patch Intelligence, Blackberry, CrowdStrike Falcon Spotlight for Vulnerability Management and others.
Time to see cybersecurity spending as a business decision. Healthcare providers need to see cyber security spending as a business investment in reducing risk. With attackers seeing their industry as one of the softest and most lucrative targets, there’s an urgent need to define the business value of cybersecurity over and above an expense – it’s an investment.
Baer told VentureBeat, “Remember that ransomware is generally money motivated (though sometimes nation-state backed). The fact that UnitedHealth paid the ransom indicates that the attackers picked a ripe target.”
VentureBeat’s mission is to be a digital town square for technical decision-makers to gain knowledge about transformative enterprise technology and transact. Discover our Briefings.
[ad_2]
Source link